"Do we really need this?"
Do you and your team have a good password management system set up? Are you certain that all logins related to your business have unique, randomly generated passwords with 30+ characters and digits, or could people still be cutting corners with certain logins, using passwords related to a favorite person or place? In this day and age, chances are that if you use a password that you easily remember, your account would be a piece of cake to hack into if a hacker cared enough to try.
"Got one, don't need help" Well...
In case your organization already uses a good password manager application, are there good systems in place for sharing vaults, syncing across browsers and devices, backing up data, implementing security audits, insightfully organizing logins and increasing productivity? Perhaps even more critically, are there good emergency procedures in place in case the only person who had access to a critical resource becomes unavailable or incapacitated?
"Boosting productivity and security, yes. But engagement?"
Everyone loves good systems and seamless user experiences (and yes, these systems unquestionably reduce risk and save you time), but can a fresh approach to organizing online accounts actually make people more engaged with their work? Absolutely. In the past five years of developing innovative procedures we've seen time and again just how much our methods work as a breath of fresh air, helping people transition from frustration and overwhelm to confidence and inspiration. That is after all the sole purpose of everything we do here at the Freedom Lovin Community – to help you master the unruly world of matter, so that you can reach a lasting state of inner peace and freedom, the very source of creativity and inspiration.
? An unprecedented journey
Every organization has different needs and styles, resources and capabilities, priorities and challenges. We tailor our services to meet your specific context, whether you have no existing systems in place or have a thriving IT department with highly effective procedures in place. While this journey starts off with implementing solid structures and correcting old habits, we guide experienced "players" towards ever increasing creativity, collaboration and inspiration – a foreign language in the world of password management systems!
Act 1 ? The Saturn V Propeller
If you don't yet have a good system in place, we will help you implement one step-by-step.
First Stage ? Choose the right application
- Compare the features and costs of different password manager applications.
- Use the collective experience of the Freedom Lovin Community to avoid disappointing applications.
- Examine specific workflows, team behaviors and security needs in your organization.
- Evaluate which option best fits your financial and operational needs.
Second Stage ☁️ Set up the software correctly
- Choose a master password using insight garnered from years of experience, research and creative thinking by the Freedom Lovin Community. Coach team members to do the same.
- Choose between cloud options, set up backup connections and go crazy increasing security with our carefully developed strategies.
- Ensure that all team members have their devices and browsers syncing correctly – otherwise they won't use it.
Third Stage ? Change passwords for all accounts
- Evaluate options for coaching team members or designating a point person to change passwords for all accounts.
- Understand password recipes and restrictions, balancing security with expediency.
- Make decisions about double-factor authentication, evaluating usage levels and degrees of importance.
- Establish procedures for creating new logins, implementing regular audits and ensuring adoption by team members.
Act 2 ? The Command Module
If your organization already employs a good password management system, but you suspect there may be security or procedural weaknesses in how you use it, you will love our personalized recommendations.
? Adjust access levels
- Determine who should have access to which vital resource, and calibrate permissions accordingly.
- Develop the correct strategy for vaults – evaluating each vault's purpose, usage and sharing needs.
- Decide where each vault's cloud-based password should be kept, and who should have access to it.
? Shore up potential vulnerabilities
- Establish procedures for security audits, examining logins, team usage patterns and the password manager's current setup.
- Examine syncing and backup connections, and consider our randomization and concealment strategies to bolster security.
- Evaluate the different approaches used to create a master password, to share resources, and to sign in to password managers on different devices and browsers.

? Examine your traces
- Move sensitive company information to secured vaults. Use our comprehensive list to ensure all information is secure but easily accessible during normal operations and in emergency circumstances.
- Delete unused accounts and clean up your digital traces.
- Stay informed about website vulnerabilities and hacks, and take appropriate counter-measures.
Act 3 ? The Lunar Module
For organizations that already have a good handle on this stuff, the next step is infusing this whole process with creativity and personal empowerment.
Descent Stage ? Enter a different environment
- Get the full picture on browser password behaviors, autofill and private browsing, keychain and other managers, and form the right strategy.
- Adopt a winning strategy on two-factor authentication options.
- Instruct your team about the structure of URLs and on how and when they should be entered into the password manager.
- Adopt intelligent policies on separating personal from work-related information and accounts.
- Get people to stop taking notes in places where they will never find what they need, when they need it.
The Rover ? Explore a new place
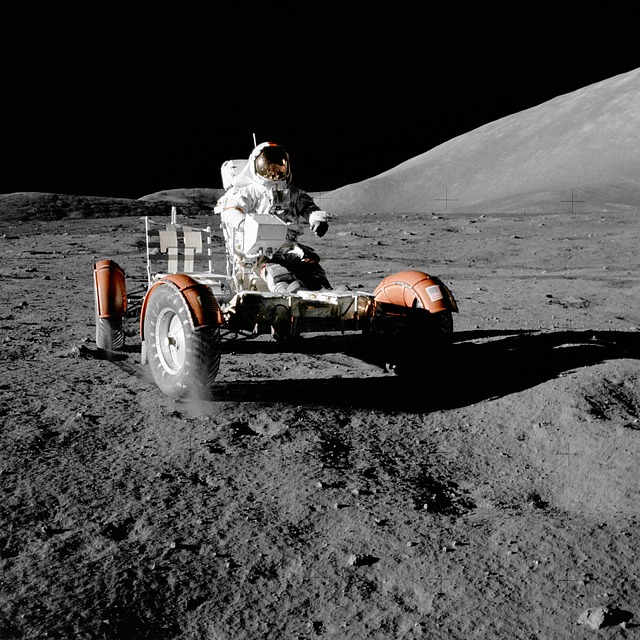
- Teach your team to organize their work in creative and insightful ways using a password manager.
- Use our proven techniques to reduce time wastage, confusion and frustration as people take full responsibility for their digital presence.
- Make use of tags and categories, vaults and favorites, keyboard shortcuts and intelligent descriptions in a way that actually saves you time, instead of increasing complexity.
- Try out our methods to stimulate the right brain as you go about your work, all while simplifying content and tasks.
Ascent Stage ? Secure the way back
- Skip the enormous hassle and stress of losing access to vital resources, while ensuring that the only the right people gain access to privileged information and assets.
- Adopt company-wide procedures for gaining access to private vaults in case employees get hacked, forget their master passwords, leave disgracefully or become incapacitated.
- Employ proper legal counsel and incorporate the necessary policy descriptions in employee and partner contracts.
- Set up procedures and legal foundations for taking over accounts, vaults or devices if undesirable conditions arise.
- Learn about the Freedom Lovin Community's pioneering approach to "achieving rendezvous," using a system that ensures privacy and security, but also successful reintegration when a series of conditions is met.